Обзор
Casdoor построен на основе OAuth и использует токены как OAuth-токены пользователей.
Access Token and ID Token
In Casdoor, the access_token and id_token are identical. Both tokens contain the same JWT payload with user information and claims. This is a design choice in Casdoor that simplifies token management.
This approach means:
- Both tokens contain the same user information and custom claims
- Both tokens can be used interchangeably for authentication and authorization
- The token format and expiration settings apply to both tokens equally
- You cannot configure separate claims for
access_tokenandid_token
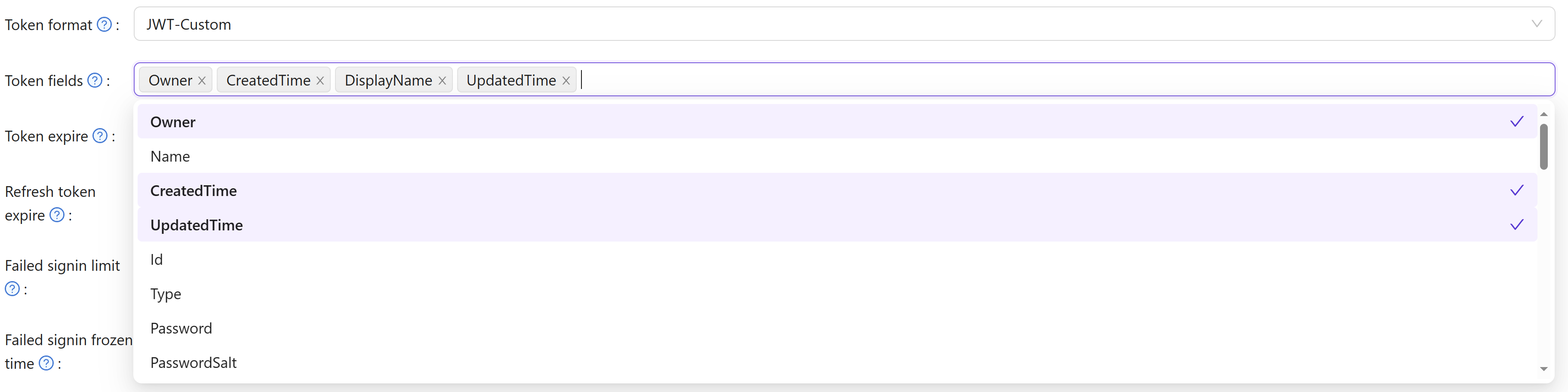
Token Fields
Ниже приведены доступные поля токенов в Casdoor:
OwnerNameCreatedTimeApplicationOrganizationUserCodeAccessTokenExpireIn(Токены истекают через часы)Scope(Область авторизации)TokenType(например, типBearer)
После входа в приложение есть три варианта генерации JWT-токена:
JWTJWT-EmptyJWT-CustomJWT-Standard
Варианты следующие: JWT сгенерирует токен, содержащий все поля пользователя, JWT-Empty сгенерирует токен со всеми непустыми значениями для пользователя, и JWT-Custom сгенерирует токен, содержащий настраиваемые поля токена пользователя (вы можете выбрать атрибуты в полях токена). JWT-Standard will generate a token with some standard OIDC token fields include email, phone, gender and Address (Address value in other format is not standard).
Custom Token Attributes
When using JWT-Custom format, you can define custom attributes with their data types. Each attribute has a Type field that controls how values are included in the JWT:
- Array: The attribute value will always be returned as an array, even if it contains a single element. This ensures compatibility with OIDC clients that expect array types for fields like roles, groups, or permissions.
- String: The attribute value will be returned as a single string (the first element if multiple values exist).
Empty attributes are automatically omitted from the token to keep the payload clean. When configuring attributes for roles, groups, or permissions, using the Array type is recommended for better OIDC compliance and compatibility with systems like Rancher and Keycloak.