Tencent Cloud (SAML)
This guide configures Casdoor as a SAML identity provider for Tencent Cloud (CAM).
Get SAML metadata from Casdoor
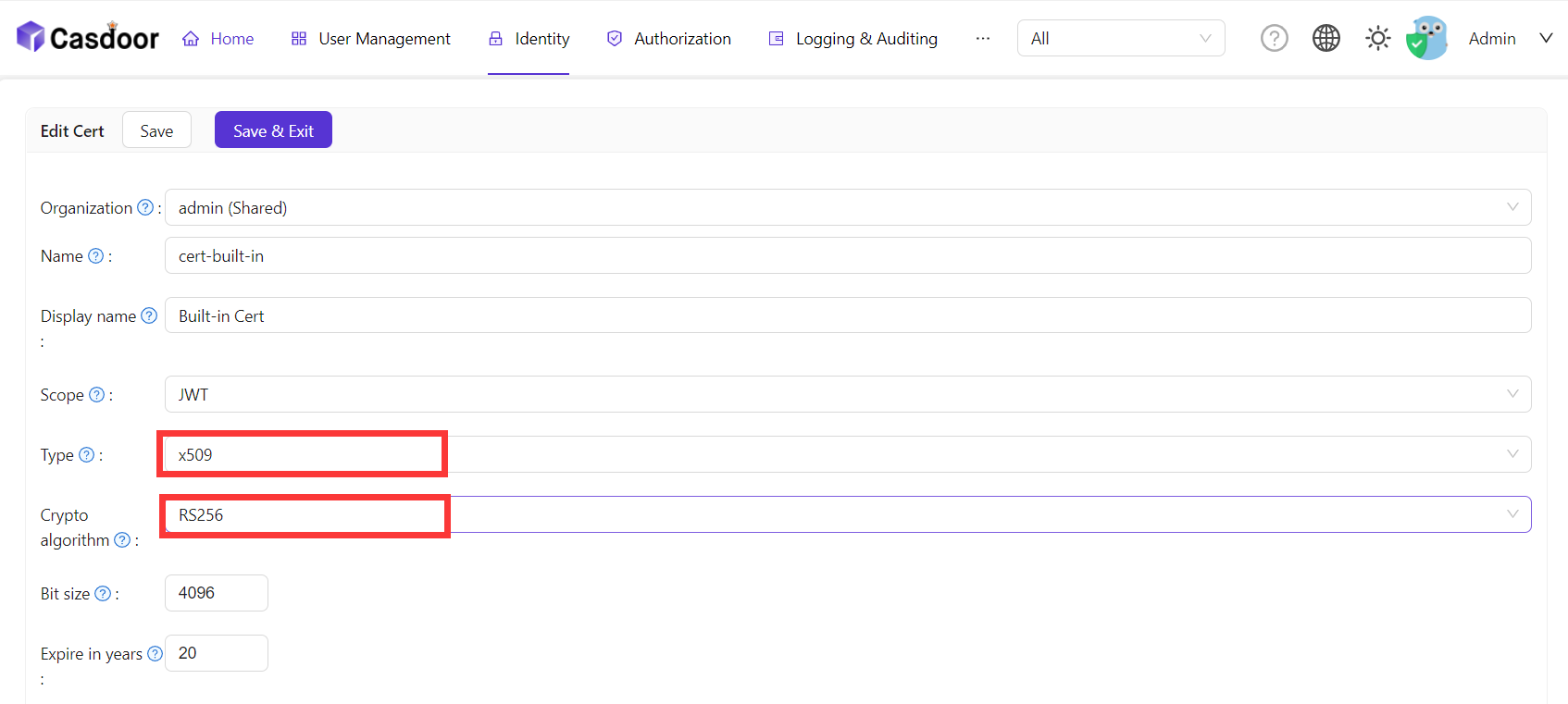
- In Casdoor, add an X.509 certificate (RSA).
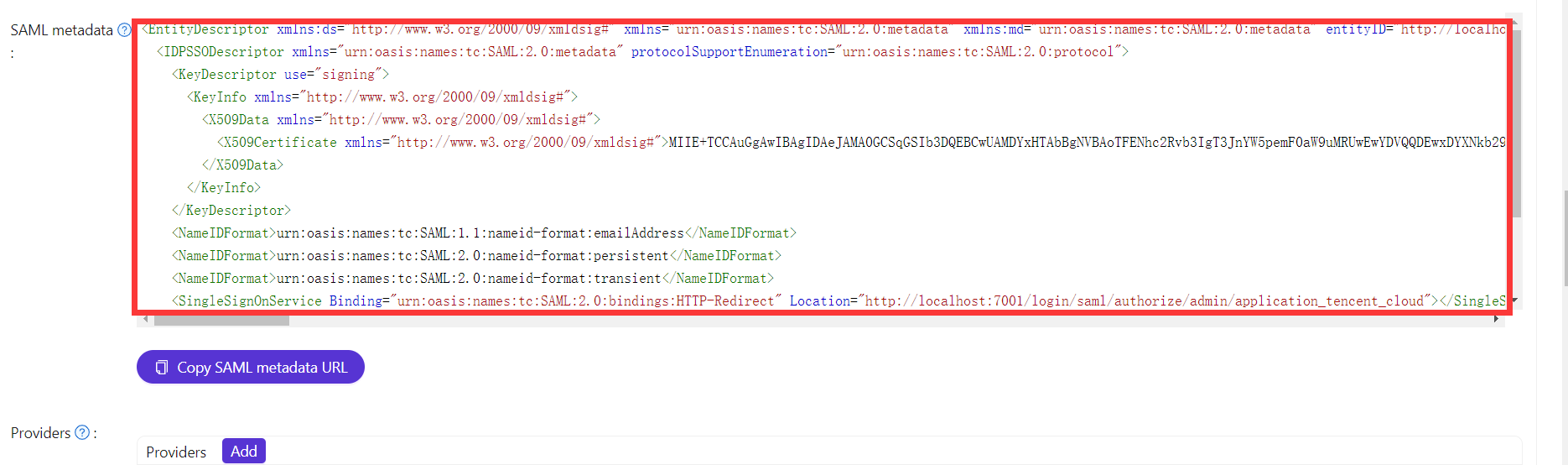
- Copy the SAML metadata from the application (or metadata URL).
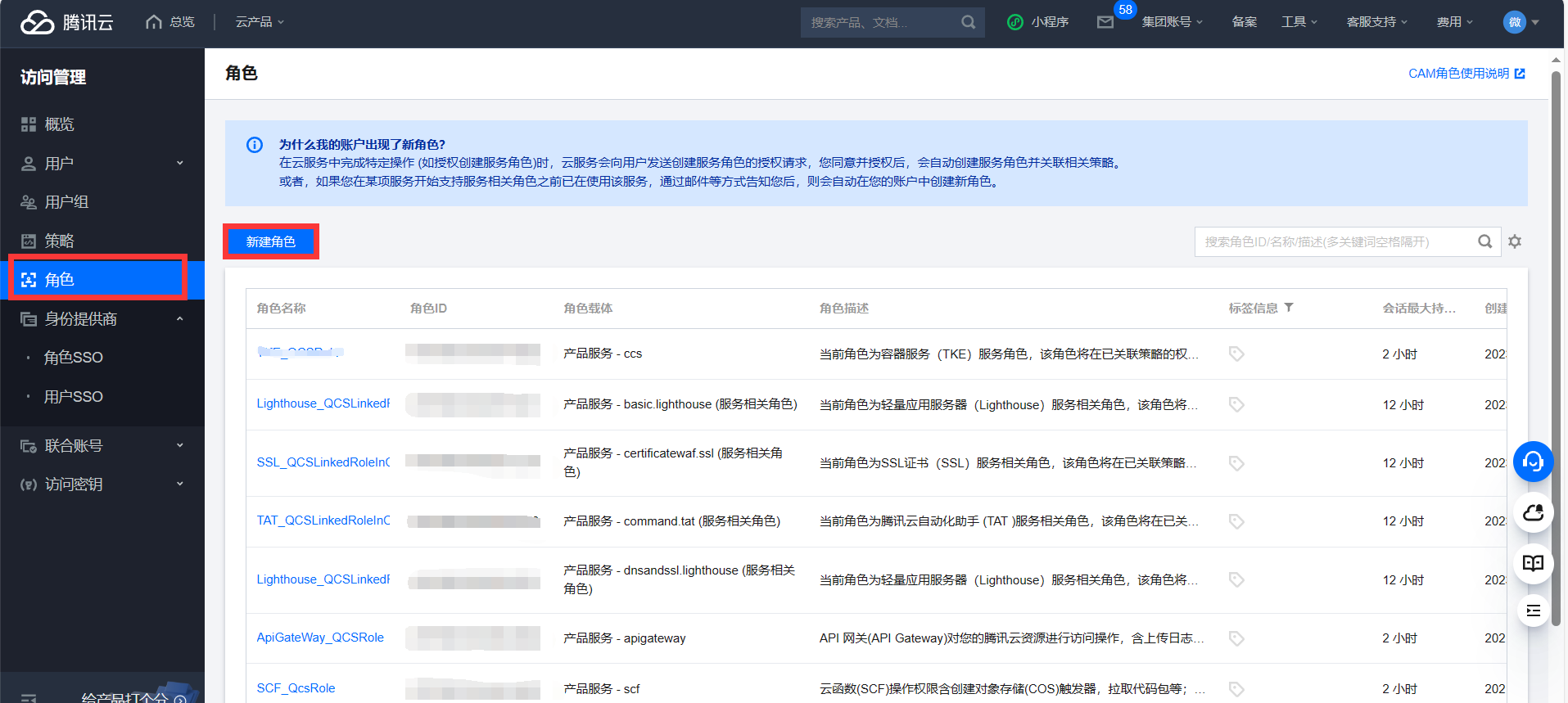
Add SAML IdP and role in Tencent Cloud
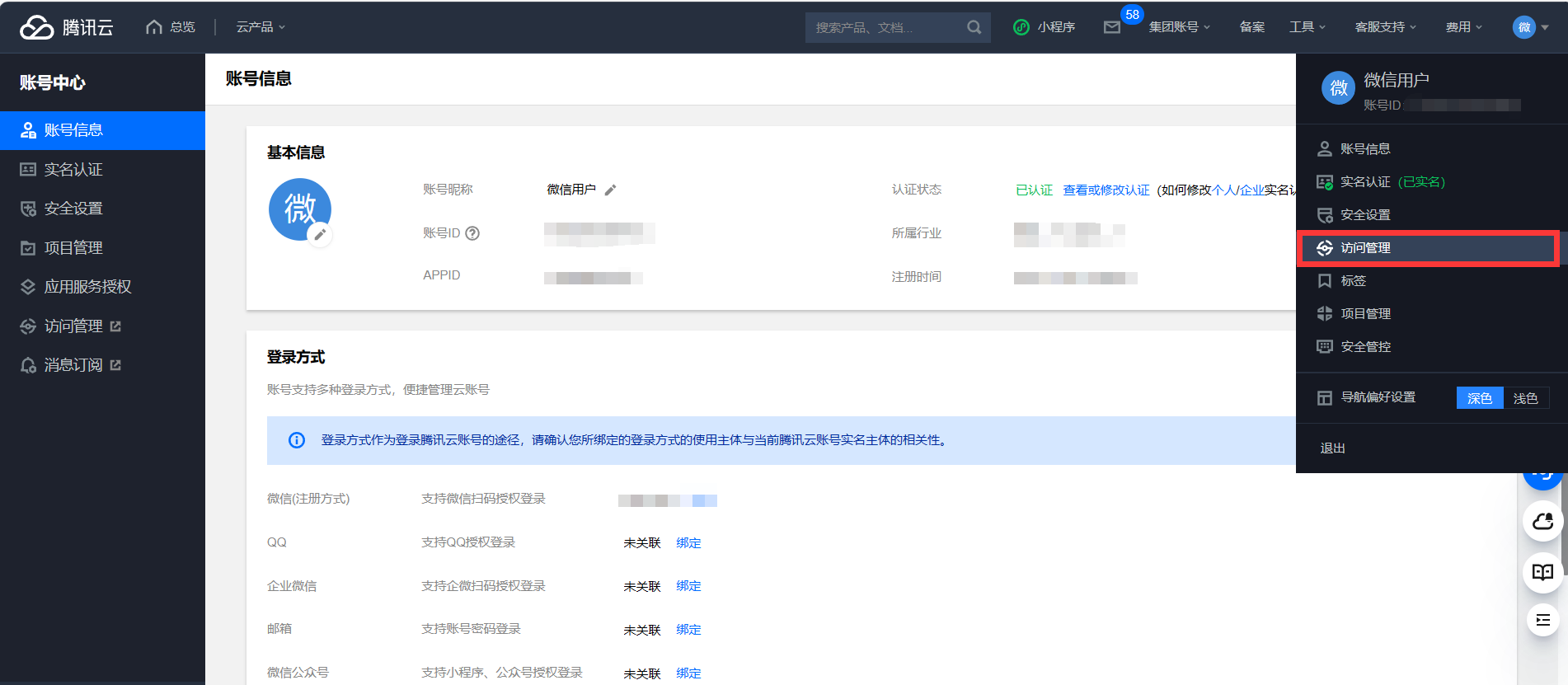
- Log in to Tencent Cloud and open Access Management (CAM).
- Create a new Identity provider and upload the Casdoor SAML metadata.
- Create a new Role and select that identity provider.

Configure the application in Casdoor
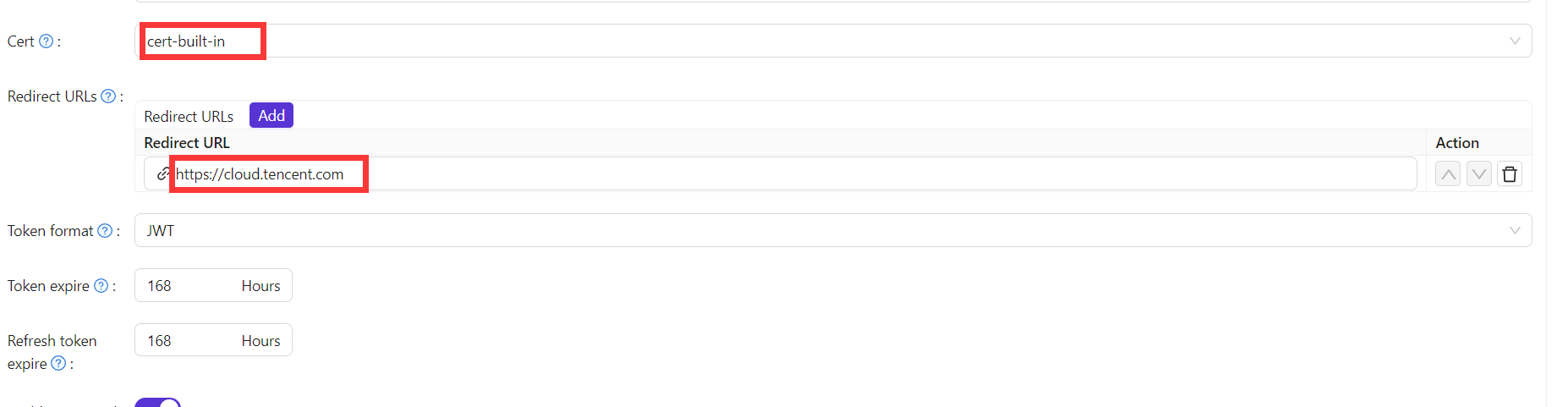
- On the application edit page, select the certificate and add the Tencent Cloud domain to Redirect URLs.
- Set the ACS URL and configure SAML attributes as follows:
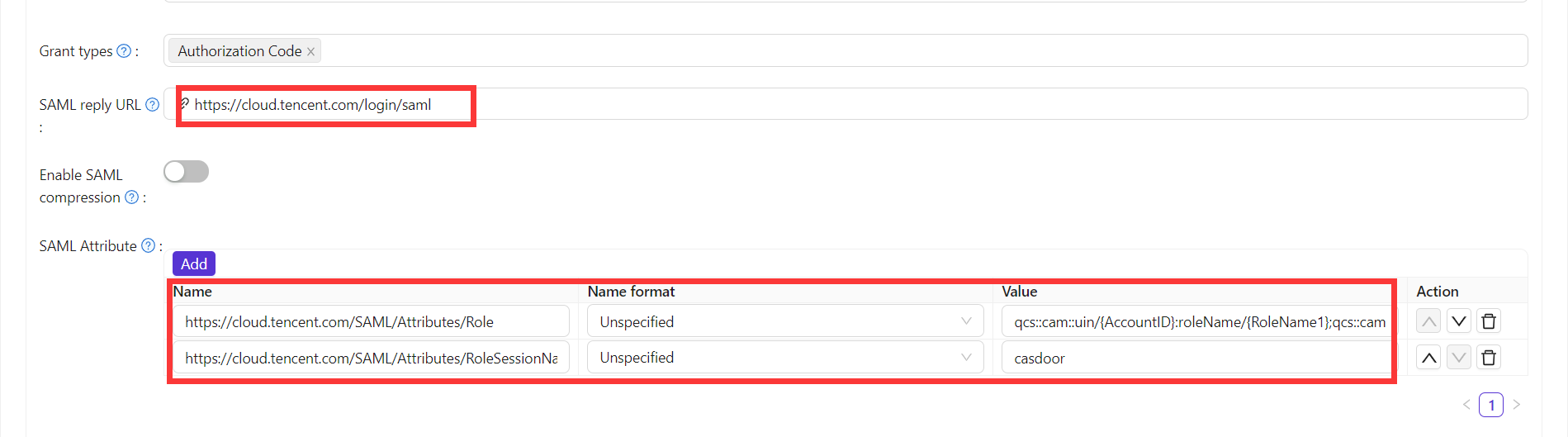
| Nom | Format du nom | Valeur |
|---|---|---|
https://cloud.tencent.com/SAML/Attributes/Role | Non spécifié | qcs::cam::uin/{'{'}AccountID{'}'}:roleName/{'{'}RoleName1{'}'};qcs::cam::uin/{'{'}AccountID{'}'}:roleName/{'{'}RoleName2{'}'},qcs::cam::uin/{'{'}AccountID{'}'}:saml-provider/{'{'}ProviderName{'}'} |
https://cloud.tencent.com/SAML/Attributes/RoleSessionName | Non spécifié | casdoor |
info
Replace placeholders using:
- {AccountID}: Tencent Cloud account ID — Account Information
- {RoleName}: Role name — Roles
- {ProviderName}: SAML identity provider name — Identity Providers
Log in via SAML
Flow: User → Tencent Cloud (unauthenticated) → redirect to Casdoor → sign in → Tencent Cloud (authenticated). The initial redirect URL can be built from SAML metadata and IdP SSO URL. Example (Go) that fetches metadata, builds the auth URL, and prints it:
func main() {
res, err := http.Get("your casdoor application saml metadata url")
if err != nil {
panic(err)
}
rawMetadata, err := ioutil.ReadAll(res.Body)
if err != nil {
panic(err)
}
metadata := &types.EntityDescriptor{}
err = xml.Unmarshal(rawMetadata, metadata)
if err != nil {
panic(err)
}
certStore := dsig.MemoryX509CertificateStore{
Roots: []*x509.Certificate{},
}
for _, kd := range metadata.IDPSSODescriptor.KeyDescriptors {
for idx, xcert := range kd.KeyInfo.X509Data.X509Certificates {
if xcert.Data == "" {
panic(fmt.Errorf("metadata certificate(%d) must not be empty", idx))
}
certData, err := base64.StdEncoding.DecodeString(xcert.Data)
if err != nil {
panic(err)
}
idpCert, err := x509.ParseCertificate(certData)
if err != nil {
panic(err)
}
certStore.Roots = append(certStore.Roots, idpCert)
}
}
randomKeyStore := dsig.RandomKeyStoreForTest()
sp := &saml2.SAMLServiceProvider{
IdentityProviderSSOURL: metadata.IDPSSODescriptor.SingleSignOnServices[0].Location,
IdentityProviderIssuer: metadata.EntityID,
ServiceProviderIssuer: "https://cloud.tencent.com",
AssertionConsumerServiceURL: "https://cloud.tencent.com/login/saml",
SignAuthnRequests: true,
AudienceURI: "https://cloud.tencent.com",
IDPCertificateStore: &certStore,
SPKeyStore: randomKeyStore,
}
println("Visit this URL To Authenticate:")
authURL, err := sp.BuildAuthURL("")
if err != nil {
panic(err)
}
println(authURL)
}
After running the code, open the printed URL to test login.