GitLab
Casdoor는 OIDC 프로토콜을 사용하여 자체 배포된 GitLab 서버에 연결할 수 있으며, 이 문서에서는 그 방법을 보여줍니다.
GitLab 문서에 따르면, GitLab은 HTTPS를 사용하는 OpenID 제공자만 작동하므로, SSL 인증서 설정이 있는 NGINX 리버스 프록시 뒤에 Casdoor를 배포하는 등의 방법으로 Casdoor를 HTTPS로 배포해야 합니다. Casdoor 자체는 기본적으로 HTTP를 통해 8000 포트에서만 수신하며 HTTPS 관련 기능이 없습니다.
다음은 설정에서 언급된 일부 이름입니다:
CASDOOR_HOSTNAME: Casdoor 서버가 배포된 도메인 이름 또는 IP, 예를 들어, https://door.casbin.com.
GITLAB_HOSTNAME: GitLab이 배포된 도메인 이름 또는 IP, 예를 들어, https://gitlab.com.
단계 1: Casdoor와 GitLab 배포
먼저, Casdoor와 GitLab을 배포해야 합니다.
성공적인 배포 후에는 다음을 확인해야 합니다:
- Casdoor에 로그인하고 정상적으로 사용할 수 있습니다.
- Casdoor의
origin값을 (conf/app.conf)CASDOOR_HOSTNAME으로 설정하세요.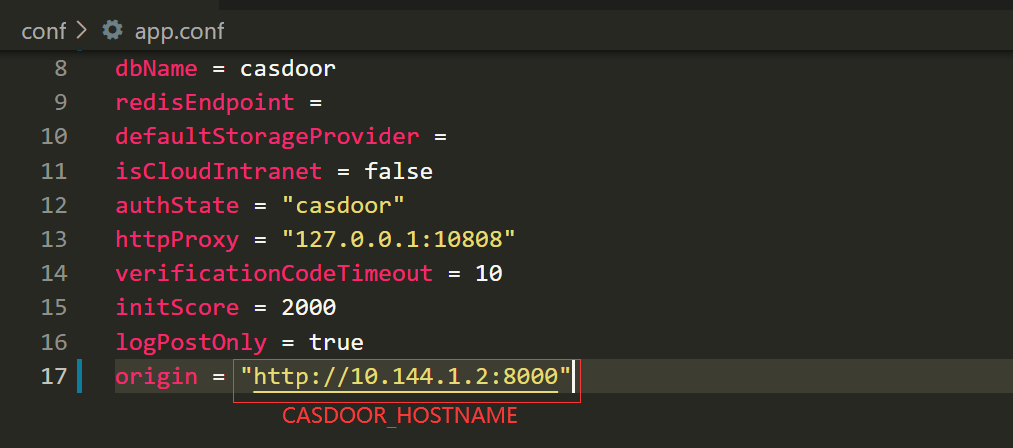
단계 2: Casdoor 애플리케이션 구성
- 기존의 Casdoor 애플리케이션을 생성하거나 사용하세요.
- 리디렉트 URL을 추가하세요:
http://GITLAB_HOSTNAME/users/auth/openid_connect/callback. - 원하는 제공자를 추가하고 다른 설정을 보완하세요.
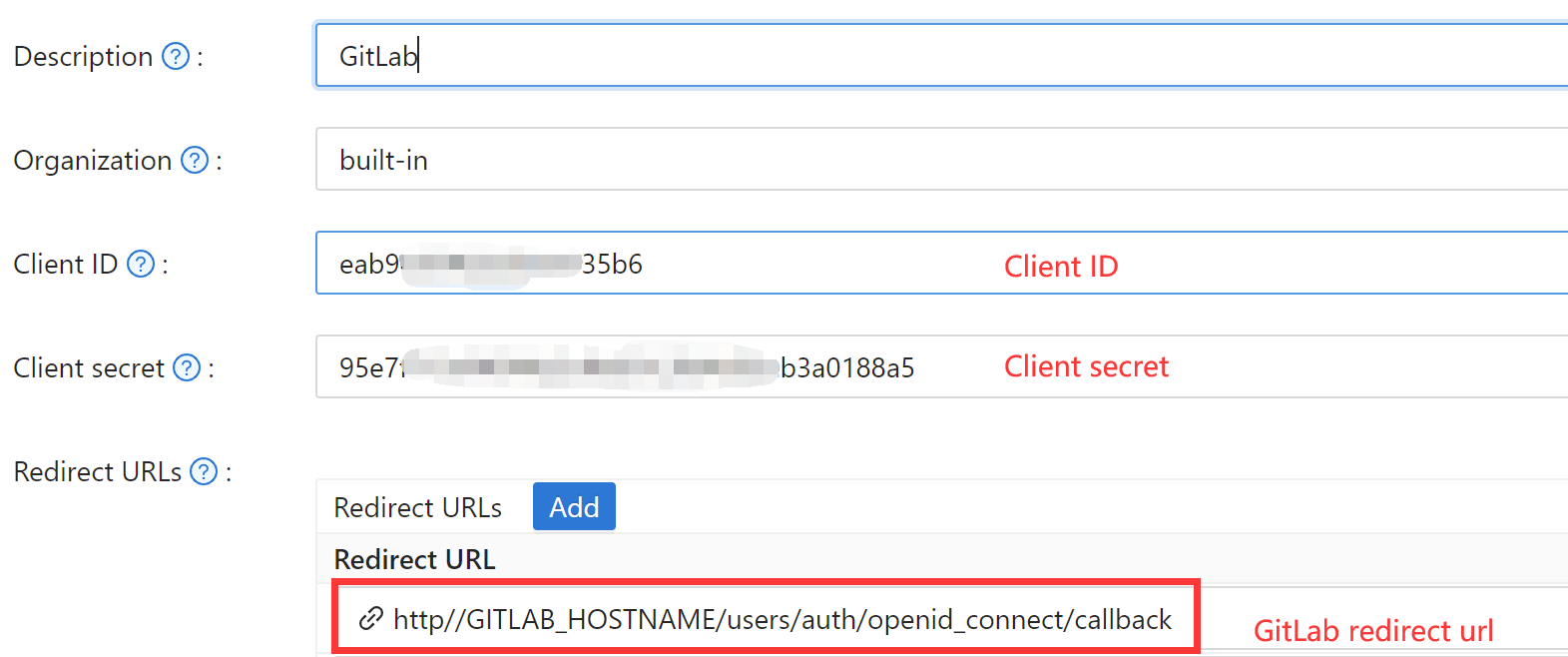 특히, 애플리케이션 설정 페이지에서
특히, 애플리케이션 설정 페이지에서 Client ID와 Client secret 두 가지 값을 얻을 수 있습니다(위의 그림 참조), 그리고 다음 단계에서 이들을 사용할 것입니다.
선호하는 브라우저를 열고 http://CASDOOR_HOSTNAME/.well-known/openid-configuration을 방문하세요. 여기에서 Casdoor의 OIDC 설정을 볼 수 있습니다.
단계 3: GitLab 구성
You can follow the steps below to set this up, or make custom changes according to this document (e.g., if you are installing GitLab using source code rather than the Omnibus).
GitLab 서버에서 설정 파일을 엽니다.
sudo editor /etc/gitlab/gitlab.rb제공자 설정을 추가하세요. (HOSTNAME URL은 http 또는 https를 포함해야 합니다)
gitlab_rails['omniauth_providers'] = [
{
name: "openid_connect",
label: "Casdoor", # optional label for the login button, defaults to "Openid Connect"
args: {
name: "openid_connect",
scope: ["openid", "profile", "email"],
response_type: "code",
issuer: "<CASDOOR_HOSTNAME>",
client_auth_method: "query",
discovery: true,
uid_field: "preferred_username",
client_options: {
identifier: "<YOUR CLIENT ID>",
secret: "<YOUR CLIENT SECRET>",
redirect_uri: "<GITLAB_HOSTNAME>/users/auth/openid_connect/callback"
}
}
}
]GitLab 서버를 재부팅하세요.
각 등록된 사용자는
GITLAB_HOSTNAME/-/profile/account를 열고 Casdoor 계정을 연결할 수 있습니다.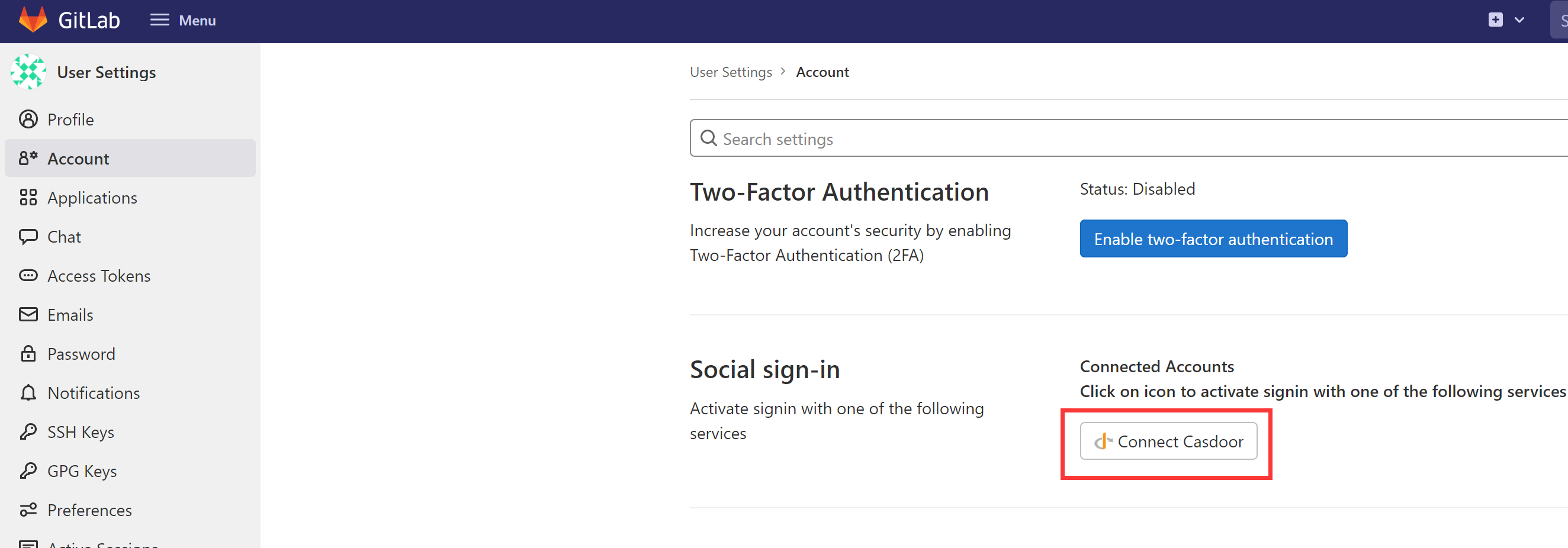
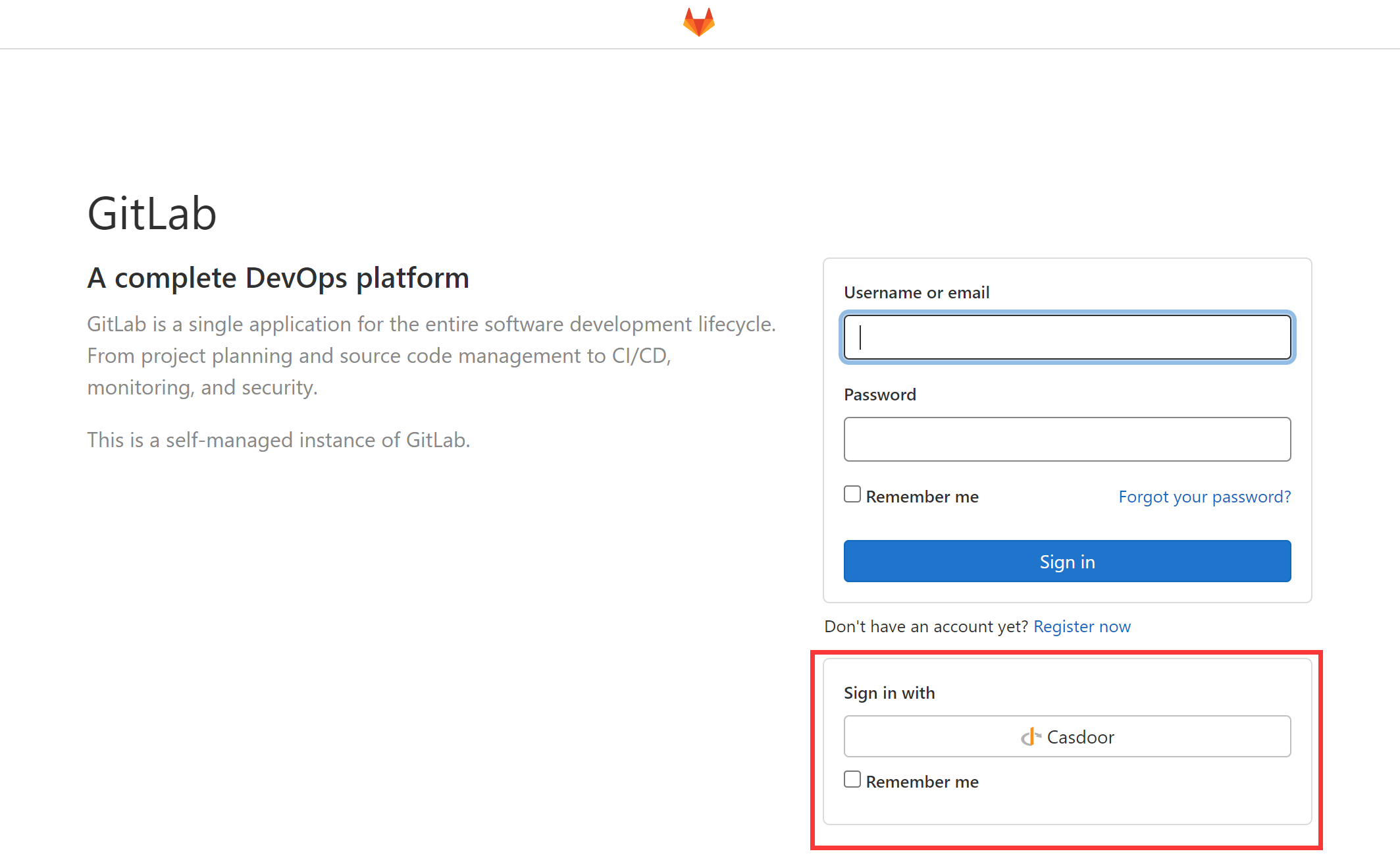
완료. 이제 Casdoor를 사용하여 자신의 GitLab에 로그인할 수 있습니다.