Appgate (SAML POST)
Appgate accepts SAMLResponse via POST. This guide applies when using Casdoor as the SAML IdP for Appgate (and for other SPs that support POST).
Casdoor configuration
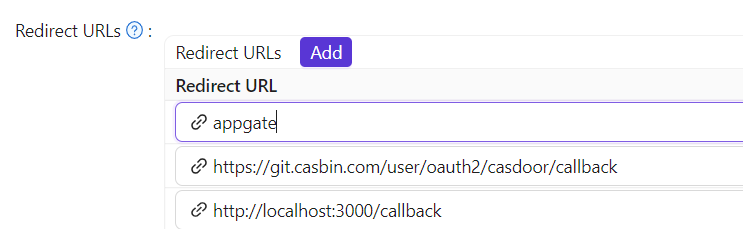
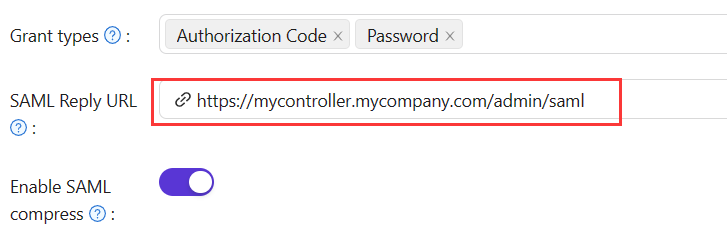
Create or edit the application in Casdoor and set:
| Setting | Value |
|---|---|
| Redirect URL | Unique identifier (Audience/Entity ID in the SP). Use the value from the table below. |
| 返信URL | ACS URL that receives and verifies the SAML response. |
| Use case | Redirect URL | SAML Reply URL |
|---|---|---|
| Administrator auth | AppGate | https://mycontroller.your-site-url.com/admin/saml |
| User auth | AppGate Client | https://redirectserver.your-site-url.com/saml |
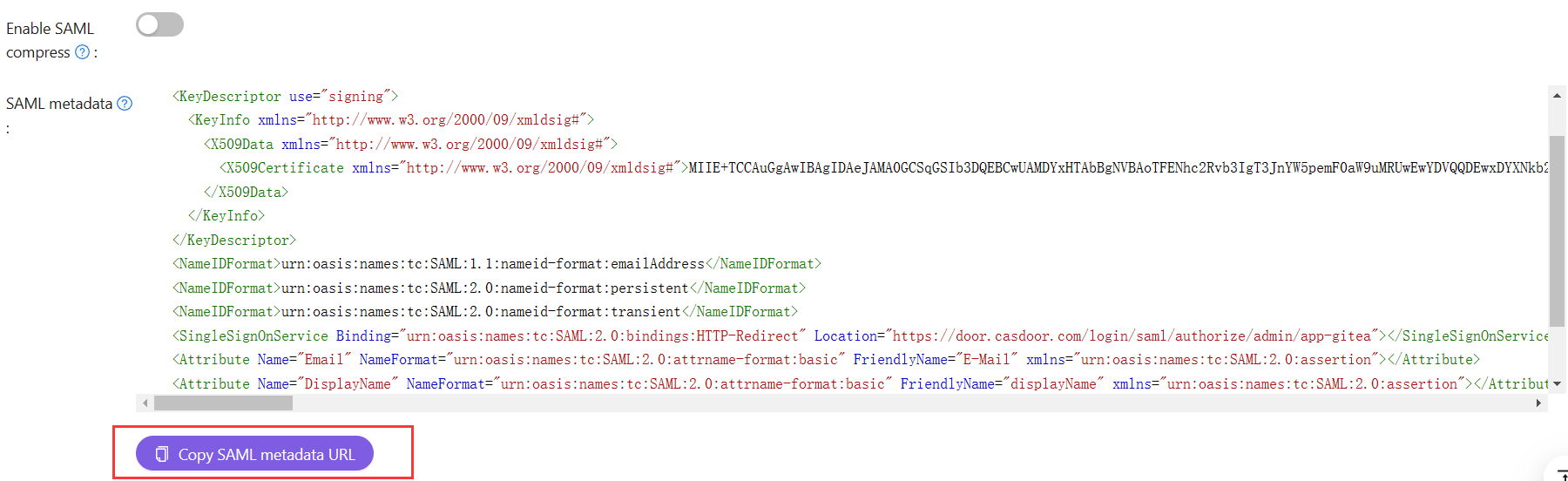
Download the SAML metadata (copy the metadata URL and open it in a browser to save the XML).
AppgateにSAML IdPを追加する
- In AppGate SDP Console → System → Identity Providers, create a new provider and choose SAML.
- Set Name (e.g. "Casdoor SAML Admin"). For Single Sign-on URL, Issuer, and Public Certificate, upload the metadata file so they are filled automatically.
- Set Audience to the Redirect URL you configured in Casdoor.
Upload the metadata via Choose a file to autocomplete Single Sign-On URL, Issuer, and Public Certificate.
Map attributes
Map the Name attribute to username.
Test
- Log out of the AppGate admin UI.
- Sign in with Identity Provider set to your Casdoor IdP and Sign in with browser.
- A message like "You don't have any administration rights" indicates the IdP authenticated the user; adjust Appgate roles/policies as needed.
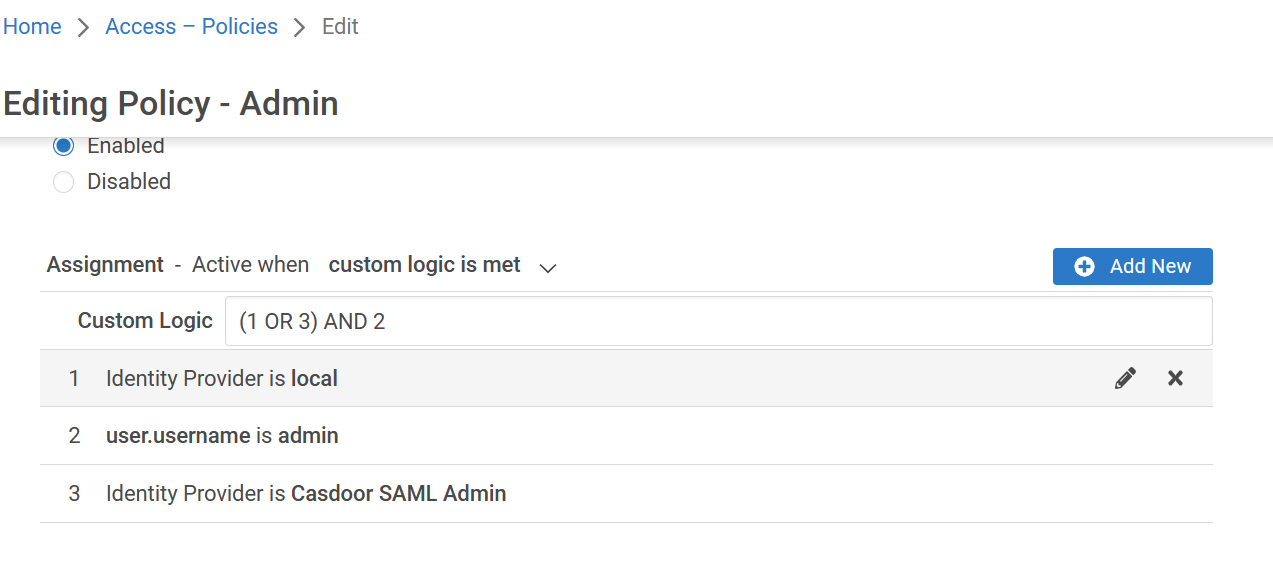
Access policy
Update the Builtin Administrator Policy (or equivalent) so administrators can sign in via the SAML IdP.